Anatomy of a hack: Examining Root The Box’s attack on UVA’s website
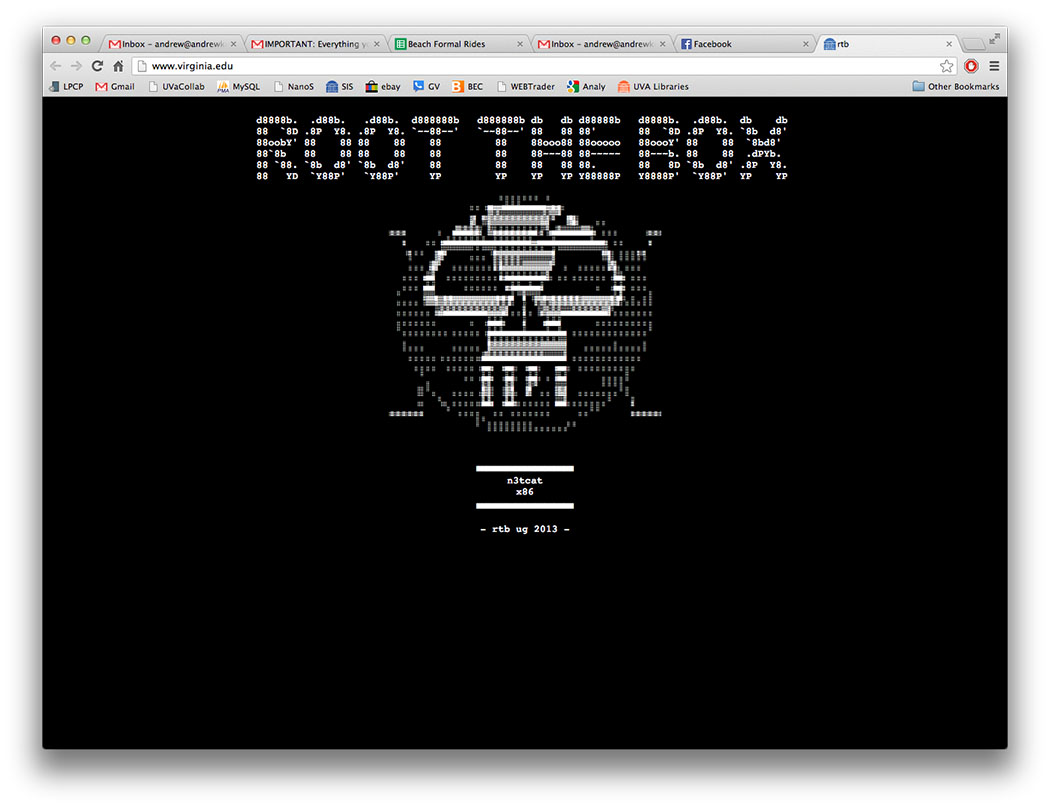
This screenshot from UVA third-year Andrew Kouri’s computer shows last week’s UVA homepage hack in real time.
Support C-VILLE Weekly
C-VILLE Weekly is Charlottesville’s leading newspaper. Founded in 1989, it’s been the area’s local source for informative (and informed) stories in news, arts, and living for more than 26 years.
UP NEXT
The Big Picture
Price of prevention
Green speak
In brief
IN CASE YOU MISSED IT
The Big Picture
Price of prevention
Green speak
In brief
PUBLICATIONS
C-VILLE Weekly | April 17, 2024
C-VILLE Weekly | April 10, 2024
C-VILLE Weekly | April 3, 2024
C-VILLE Weekly | March 27, 2024
Real Estate Weekly | April 17, 2024
Real Estate Weekly | April 10, 2024
Real Estate Weekly | April 3, 2024
Real Estate Weekly | March 27, 2024
Knife & Fork | Spring/Summer 2024
Fine Properties | Spring 2024
Abode | Winter 2024
Weddings | Fall/Winter 2023
Best of C-VILLE 2023
We Are C-VILLE | March 2024
Summer Camp Guide | March 2024
National Nonprofit Day | August